Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cybersecurity Awareness Month: Top Trends Impacting Your Applications
It’s always important to take a pause to evaluate your software security – and what better time to do that than during Cybersecurity Awareness Month? To help get you thinking, we’ve compiled a list of cybersecurity trends that are happening now and will likely continue throughout the next several years. 1. Ubiquitous Connectivity: We are quickly moving to a world where everyone and everything is connected. Most software is internet-connected, as are most devices.
Software Composition Analysis Mitigates Systemic Risk in the Popular NPM Repository
Chris Wysopal, Veracode Chief Technology Officer and Co-Founder, recently sat down to discuss the open source supply chain attack on the popular npm repository. Below is the transcript and corresponding video of his reaction. Just a few days ago, we saw a classic open source supply chain attack where someone modified a JavaScript library, UA-Parser-JS, which is in the npm repository.
Veracode Co-Founder & CTO Chris Wysopal talks to BBC World News
.NET 5, Source Generators, and Supply Chain Attacks
Attacks executed through builds abuse trust we have in our build tools, IDEs, and software projects.
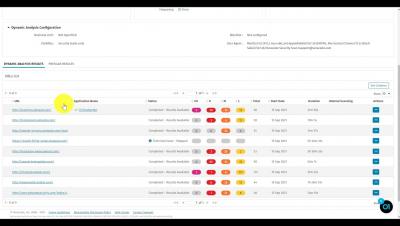
View Dynamic Analysis Results
Recap: Virtual Boston Globe Summit
Veracode CEO Sam King had the opportunity to speak at this year’s inaugural virtual Boston Globe Summit, “The Great Recovery.” Sam was invited to join the panel, How Boston is Tackling the Biggest Cyber Threats Facing Society, moderated by Gregory T. Huang, Business Editor at the Boston Globe, with guests Greg Dracon of.406 Ventures and Christopher Ahlberg of Recorded Future.
Application Security Testing Evolution and How a Software Bill of Materials Can Help
Early in my career, I developed web applications. At the time there were practically no frameworks or libraries to help. I was coding with Java using raw servlets and JSPs – very primitive by today's standards. There was no OWASP Top 10 and writing secure code was not something we paid much attention to.
MPT's Value at Veracode
You finally have some budget to buy tools for your application security (AppSec) program! GREAT! Purchasing the correct tools for your AppSec pogram can be overwhelming. Even when looking only at point solutions, there still may be some confusion on the value that various tools can provide. Sometimes you'll find the perfect tool, but others may offer you a similar tool with added manual penetration testing (MPT) as part of the overall bundle. That seems like a great idea for the budget.
2003 Testimony to Congress Proves That We Still Have a Long Way to Go In Building Secure Software
Back in May 1998, as a member of the hacker think tank, L0pht, I testified under my hacker name, Weld Pond, in front of a U.S. Senate committee investigating government cybersecurity. It was a novel event. Hackers, testifying under their hacker names, telling the U.S. government how the world of cybersecurity really was from those down in the computer underground trenches.