Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cyberstalking vs Cyberbullying vs Cyber Harassment: What's the Difference?
According to Pew Research, 41% of Americans have experienced some form of online harassment – and the severity of incidents has been getting worse over time. Understanding what different types of online harassment look like, and what behaviors harassers engage in, can help you recognize and address it. Keep reading to learn about the different types of online harassment, consequences of online harassment and how to avoid becoming a target.
Unlock 1Password with Duo, OneLogin, and more
1Password Business customers can now unlock 1Password with identity providers (IdPs) that support the generic OpenID Connect (OIDC) configuration like Duo, OneLogin, JumpCloud, and others.
Keeper Launches New Global Password Report
Keeper Security has released its latest research, Password Management Report: Unifying Perception with Reality, which assesses the password habits of individuals across the United States and Europe.
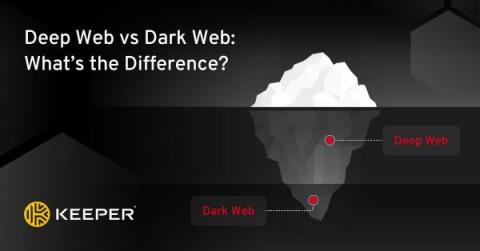
Deep Web vs Dark Web: What's the Difference?
The main difference between the deep web and the dark web is that the deep web is bigger and used every day by most people without even realizing it. The dark web can only be accessed with the Tor browser and is riskier to access than the deep web. Continue reading to learn more about the differences between the deep and dark web, and how you can keep your information protected from both.
Securing CI/CD pipelines with 1Password Service Accounts
Attention developers and DevOps teams! Today we’re excited to announce that 1Password Service Accounts are now generally available to all users. Whether you’re a growing startup, a thriving mid-size company, or a sprawling enterprise, service accounts offer a secure, automated way to access infrastructure secrets exactly where they’re needed.
New: Manage accounts directly from the 1Password app
Coming to iOS later this week and available today on macOS, Windows, Linux, and Android, manage invites, guests, and more – all directly from the 1Password app.
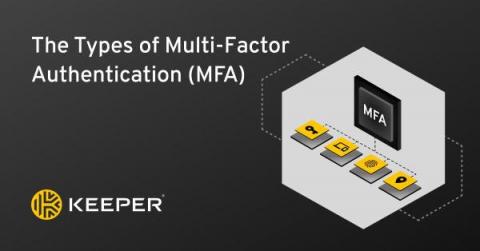
Types of Multi-Factor Authentication (MFA)
The four types of Multi-Factor Authentication (MFA) are knowledge, possession, inherence and location. These authentication types provide a foundation for a number of MFA methods, giving users multiple options for securing their data, ranging from SMS message tokens to hardware security keys. Which method is right for you or your business can depend upon what you have access to and how secure you want to be.