Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Software Supply Chain Security: The Basics and Four Critical Best Practices
Enterprise software projects increasingly depend on third-party and open source components. These components are created and maintained by individuals who are not employed by the organization developing the primary software, and who do not necessarily use the same security policies as the organization. This poses a security risk, because differences or inconsistencies between these policies can create overlooked areas of vulnerability that attackers seek to exploit.
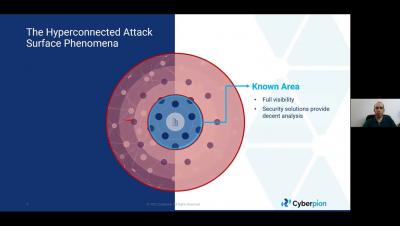
Hyperconnected External Attack Surface Protection
JavaScript supply chain issues
JavaScript code—used in 98% of all global websites–is a notable contributor to the ongoing software supply chain attack problems. In fact, vulnerable or malicious JavaScript is likely responsible for a sizable portion of the increase in attacks during 2021.
The Biggest Security Risks in Your Supply Chain in 2022
The SolarWinds supply chain attack highlighted how vulnerable supply chains are to cyberattacks. Supply chain risk mitigation has since become an essential component of risk management strategies and information security programs. To support the success of this effort, we’ve listed the top 4 supply chain security risks you need to be aware of in 2022.
Automated Software Supply Chain Attacks: Should You be Worried?
From the factory floor to online shopping, the benefits of automation are clear: Larger quantities of products and services can be produced much faster. But automation can also be used for malicious purposes, as illustrated by the ongoing software supply chain attack targeting the NPM package repository. By automating the process of creating and publishing malicious packages, the threat actor behind this campaign has taken things to a new scale.
Ep 9 Securing the Digital Supply Chain - Punit Soni, Suki
How to Mitigate Risks in Software Supply Chain Security
Trustwave's Action Response: The Lapsus$ Hacker Group Shows Us the Importance of Securing the Digital Supply Chain
Trustwave is actively tracking the threat of Lapsus$ for our clients. We encourage all organizations, especially those part of the digital supply chain, to remain vigilant and ensure that cyber best practices are implemented. We are actively investigating all unusual login behaviors for clients that use Okta. For more information on the Okta incident, please visit their blog. Trustwave does not use Okta. Actionable security recommendations for organizations can be found below.
Alert: peacenotwar module sabotages npm developers in the node-ipc package to protest the invasion of Ukraine
On March 15, 2022, users of the popular Vue.js frontend JavaScript framework started experiencing what can only be described as a supply chain attack impacting the npm ecosystem. This was the result of the nested dependencies node-ipc and peacenotwar being sabotaged as an act of protest by the maintainer of the node-ipc package.