Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
World Class AI-Enabled Cybersecurity Conference - IdentityShield Summit 2026
Discover the future of Cybersecurity at IdentityShield Summit 2026 We’re inviting you to be a part of one of the biggest and boldest AI-driven cyber events, where you’ll deep dive into innovations, witness panels. It's a premier two-day event that brings together 5000+ global IT leaders, CISOs, CTOs, developers, and cybersecurity professionals. Get ready for an action-packed 2-day event! At this event, you can.
The next identity frontier: Automating PKI and certificate management before the 47-day era arrives
Every organization operates on a foundation of identity. Whether it’s a person logging into an app, an API connecting to a service, or a container spinning up in the cloud, every interaction begins with authentication. But here’s the shift most organizations are only starting to catch up to: machines now outnumber people by more than 80 to 1. These workloads and devices all depend on digital certificates to prove who they are. Those certificates are their identities.
The CA/B Forum mandate: a catalyst for modernizing machine identity management
Modernization rarely begins without a catalyst. For organizations managing machine identities, the CA/B Forum mandate is driving a wave of change—transforming compliance pressure into momentum for lasting modernization. For more than a decade, organizations have recognized that their machine identity operations are fragile. Manual renewals, siloed ownership, and spreadsheet-driven workflows were never built for the speed and scale of modern digital business.
Privilege Creep Explained: How to Detect and Prevent It in Organizations
Invisible or hidden risks often corrupt organizations inside out. These are hard to detect and go unnoticed for a prolonged period. Privilege Creep, one such hidden risk, is a silent security gap, where there is an accumulation of inessential access rights of employees over a period of time. This could pave the way for unauthorized access and breaches.
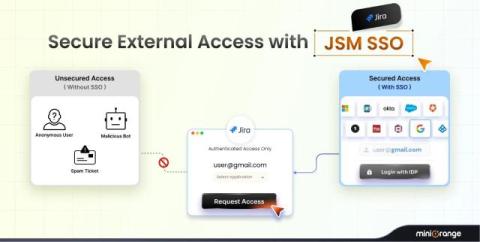
Secure External User Access in JSM: How SSO Prevents Spam Tickets
Managing external customer access in Jira Service Management (JSM) often seems straightforward, but it can create recurring problems for many teams: large volumes of spam tickets. When the customer portal allows anonymous submissions, bots and unsolicited traffic can freely enter the system, slowing support operations, affecting the customer experience, and introducing unnecessary security exposure. Teams usually see the same symptoms.
How a Government Entity Transformed Atlassian User Management with miniOrange
In the public sector, IT efficiency isn't just about convenience - it’s about fiscal responsibility and strict compliance. Government agencies often manage thousands of users across Jira, Confluence, and Jira Service Management (JSM). As these environments grow, so does the complexity of managing access.
10 IAM Best Practices for the Security of Every Enterprise 2025
Managing 5,000+ identities across your enterprise? Each one is a potential entry point for attackers—and your IAM security is only as strong as your weakest access point. This is where the most effective IAM best practices and data-driven strategies come into play.
8 Best Secure Web Gateways Of 2025
The way teams browse, work, and share data has changed fast, and so have online threats. A Secure Web Gateway (SWG) gives you a smart, always-on filter between your users and the internet, blocking malicious sites, unsafe downloads, and risky behaviors before they cause damage. With cloud apps becoming the backbone of daily operations, an SWG ensures every web request is inspected, every threat is stopped, and every employee stays protected, whether they’re in the office or working remotely.
UI Migration Guide - miniOrange SAML SSO + SCIM Provisioning App Bundle for Bitbucket
We’ve redesigned the miniOrange SAML SSO + SCIM Provisioning app for Bitbucket with a new bundled interface to make authentication and user provisioning simpler, faster, and more efficient. This video is your step-by-step guide to understanding what’s new, where to find your settings, and how to make the most of the updated dashboard. What You’ll Learn Unified Dashboard Navigation – Manage SAML SSO and SCIM provisioning from one central place.