Announcing Jit Tags: Track the security posture of your business-critical services
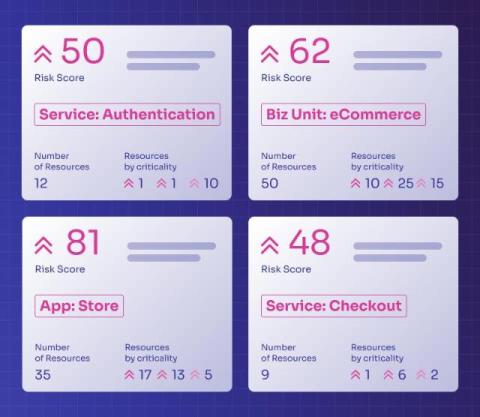
Today, we’re thrilled to announce Jit Tags, which organizes security risks across your environment by microservice, application, business unit, and other vectors, while providing a high-level risk overview of each component.