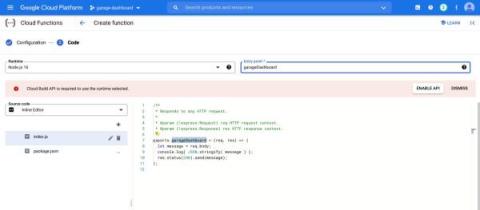
Cloud Function Dashboard with LimaCharlie
LimaCharlie provides everything you need to run modern cybersecurity operations, and it is also a great tool for builders. Our powerful web application is built using the publicly accessible API. There are no magic functions and we put the full power of the platform into the hands of those capable of wielding it. To demonstrate the kind of thing a user can easily build with LimaCharlie we have put together an interactive, embeddable dashboard.