Dissecting Image-Based Steganography in a .NET (Quasar) RAT Loader
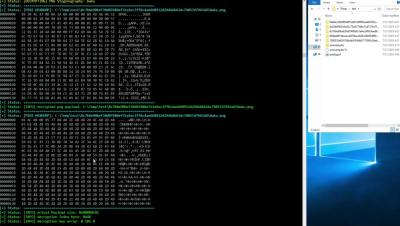
The Splunk Threat Research Team created a simple script tool to automatically extract the hidden stub modules from the resource entry images. This video demo shows how this tool can extract hidden payload on those images on non-corrupted.NET Loaders.