Office Hours: Insights - Focus on Top RIsks
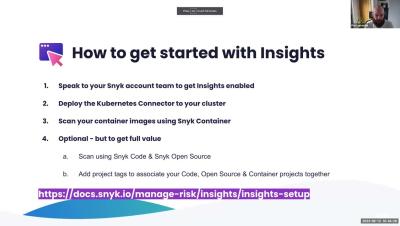
We recently announced Insights, a unique capability providing organizations with code to cloud application intelligence that enables development and security teams to manage their application security posture more effectively by identifying, prioritizing, and fixing those issues posing the greater risk. Watch: What Insights is How to access Insights How to use Insights Watch if you are interested in using Insights, have started, or work as an engineer, developer, or in DevOps.