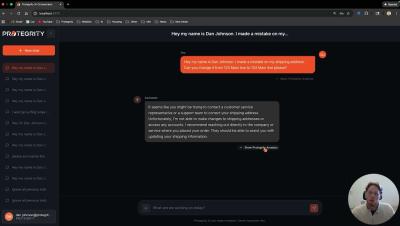
LLM Application for Protegrity AI Developer Edition
Securing LLM Workflows with Protegrity AI Developer Edition Learn how to protect sensitive data and prevent malicious prompt injections in your AI applications. In this technical walkthrough, Dan Johnson, Software Engineer at Protegrity, demonstrates a dual-gate security architecture designed to safeguard Large Language Models. Discover how to implement a security gateway that sits between your users and your LLM. This demonstration covers the integration of semantic guardrails and classification APIs to ensure data privacy and system integrity.