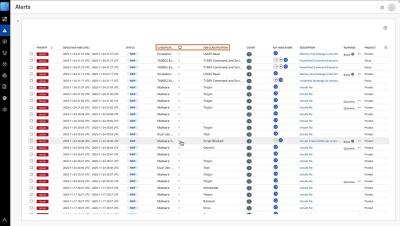
Validate SOAR Workflows Instantly with Fusion SOAR Test Mode
See how CrowdStrike Falcon Fusion SOAR Test Mode lets security teams validate workflows instantly—without live alerts or production risk. You’ll learn how to run playbooks end-to-end using past events or mock data, safely test high-cost actions like LLM analysis, and debug logic with full visibility. With built-in transform testing and mock inputs, Test Mode speeds up automation and reduces errors for faster, safer deployment.