How cert pinning and E2EE broke your CASB - and why endpoint is the new cloud control point
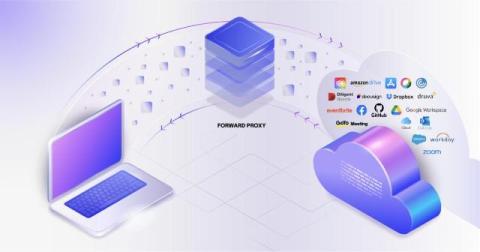
Cloud adoption among enterprises accelerated around 10 years ago. During this time, network-based tools emerged as solutions that could protect data as it traveled to the cloud. These solutions, including Security Service Edge (SSE) and Cloud Access Security Brokers (CASB), utilized network-based proxy architectures that could intercept and control traffic.