Corelight Announces Cloud Enrichment for AWS, GCP, and Azure
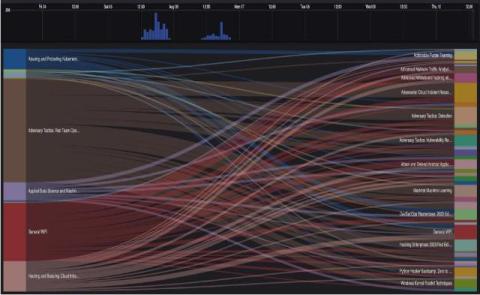
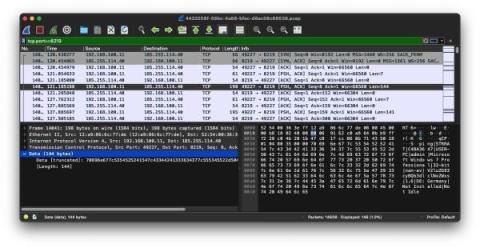
This week, I’m excited to announce Cloud Enrichment for AWS, GCP, and Azure. These enhancements are designed to accelerate incident response and unlock threat hunting capabilities by automatically combining the insights of your cloud network with the native control plane data from your cloud service provider.