Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Salt Labs exposes a new vulnerability in popular OAuth framework, used in hundreds of online services
This post is the second in a series describing OAuth implementation issues that put companies at risk. We create these posts to share rich technical details, drawn from real-world use cases, to educate the broader industry on the nature of these errors, their potential impact, and how to avoid them to better protect API ecosystems.
DigiCert Code Signing Changes: New Private Key Storage & API Modifications
Beginning on June 1, 2023, at 00:00 UTC, industry standards will mandate that private keys for code signing certificates must be stored on hardware that meets specific security certifications such as FIPS 140 Level 2, Common Criteria EAL 4+, or an equivalent standard. This requirement applies to all new code signing certificate requests and requests for renewal and reissue of existing certificates.
More Than Half of all Email-Based Cyberattacks Bypass Legacy Security Filters
New data shows that changes in cybercriminals’ phishing techniques are improving their game, making it easier to make their way into a potential victim user’s inbox. I recently wrote about how 12% of all email threats were getting all the way to the inbox. But new data from cybersecurity vendor Armorblox’s 2023 Email Security Threat Report shows that the number is much higher, depending on the security solutions in place.
BatLoader Malware is Now Distributed in Drive-By Attacks
Malign persuasion can take many forms. We tend to hear the most about phishing (malicious emails) or smishing (malicious texts). Other threats are also worth some attention, like the risk of drive-by attacks. One current drive-by campaign is being run by the operators of BatLoader, a malware strain that establishes initial entry and persistence, and then can be used to distribute a range of other malicious code that loots affected systems and networks of valuable data, including funds.
Financial Fraud Phishing Attacks Increase 72% In One Year; Financial Industry Takes the Brunt
With attackers knowing financial fraud-based phishing attacks are best suited for the one industry where the money is, this massive spike in attacks should both surprise you and not surprise you at all. When you want tires, where do you go? Right – to the tire store. Shoes? Yup – shoe store. The most money you can scam from a single attack?
EP 28 - Safeguarding Data in the Cloud
In this episode of the Trust Issues podcast, host David Puner interviews Brad Jones, CISO and VP of Information Security at Seagate Technology. They delve into cloud security challenges, including protecting data in a constantly shifting technological landscape. Jones discusses the importance of establishing trust as a data company and implementing rigorous controls to safeguard sensitive information.
EPP vs EDR - What's The Difference?
Turning Intelligence Into Action with Cybersixgill and Torq
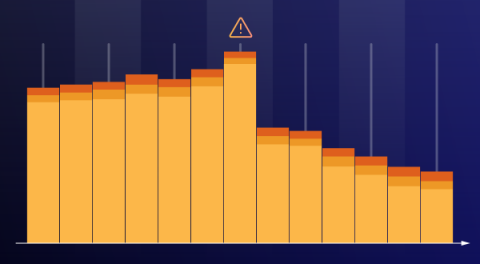
Track Risk Trends in your Container Images with Sysdig Risk-based Vulnerability Management
The number of detected common vulnerabilities and exposures (CVEs) has significantly increased in the past decade. In the last five years, security researchers reported over 100,000 new CVEs. The highest reported annual figure was in 2022, with over 25,000 new CVEs. This number can overwhelm any security team if it’s not managed correctly between assessment, reporting, remediation, and monitoring.