Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SBOMs are the gifts that keep on giving.
The timing of CISA’s SBOM-a-rama today and tomorrow coincides with the fallout from the “vulnerability of the decade” gifting the industry with yet another example of why scaling and operationalizing the widespread use of SBOMs is so vital. Log4Shell is a 10/10 vulnerability in a hugely popular Java logging library – Log4j – used in virtually every online service. For two decades it was considered harmless, that is until last week when somebody found it wasn’t.
Glide to JFrog DevSecOps with the New Experience
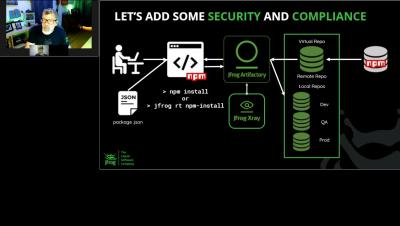
We’re excited to share with you that we have launched a completely new way to start using the JFrog DevOps Platform that you – as a developer – will love. We’ve provided a super-easy, developer-friendly path to discovering how Artifactory and Xray can help you produce safer apps, faster, getting started through the command line shell and IDE that you use every day.
Episode 1: DevSecOps Coffee Break Series Add OSS Security & Compliance to Artifactory
Episode 2: DevSecOps Coffee Break Series | Creation of Your Software Bill Of Materials SBOM
Episode 4: DevSecOps Coffee Break Series | 'Shift Left' Security With A Developer Centric Approach
Episode 5: DevSecOps Coffee Break Series | If JFrog is Good Enough For The Government, Why Not You
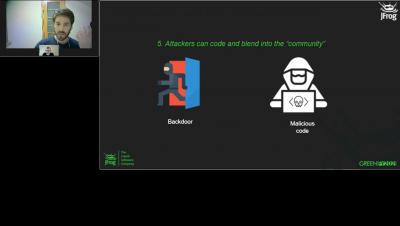
Episode 3: DevSecOps Coffee Break Series | Securing Your Software Supply Chain
SBOM Sharing Should be Easy. Now it is!
Today we’re pleased to announce the RKVST SBOM Hub – the first place to find and fetch SBOMs. RKVST SBOM Hub is a secure, immutable, any-to-any framework that integrates into both publisher and subscriber workflows to massively simplify the effective sharing of SBOMs to help all parties comply with the Executive Order. Try it out for yourself here.
Securing DevSecOps - Threat Research Release October 2021
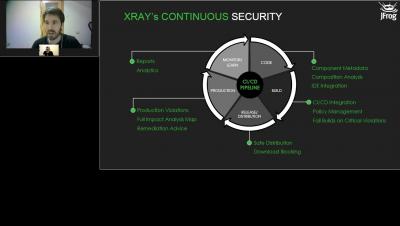
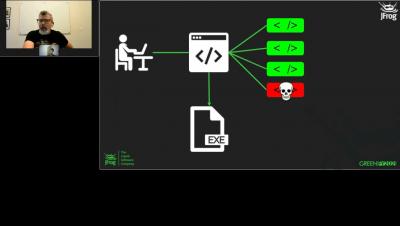
DevSecOps stands for Development, Security and Operations. This is a practice aimed to automate or design security integration throughout the software development lifecycle or workflow. Nowadays, collaborative frameworks and projects that share security protocols from end to end are really common, so DevSecOps practices attempt to emphasize building infrastructure with a strong security foundation and stable automation workflow and phases. Watch the video below to learn more about Securing DevSecOps.