What's New with JFrog Xray and DevSecOps
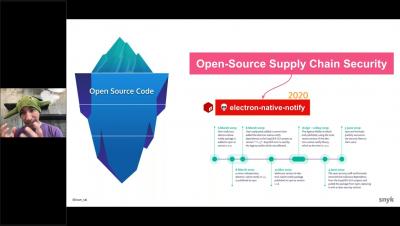
As we look to improve the quality and capabilities of the JFrog DevOps Platform, especially in the world of DevSecOps, we have added powerful new features to further enhance the award-winning JFrog Xray. The capabilities detailed below cement Xray’s position as a universal software composition analysis (SCA) solution trusted by developers and DevSecOps teams globally to quickly and continuously identify open source software vulnerabilities and license compliance violations.