Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
The Bot Left a Fingerprint: Detecting and Attributing LLM-Generated Passwords
LLMs leave statistical fingerprints in the passwords they generate. We built a 100-year-old model to find them and detected 28,000 in the wild.
The Research Behind Of Detecting And Attributing LLM-Generated Passwords - Gäetan Ferry
GitGuardian Senior Cybersecurity Researcher Gaetan Ferry’s latest research shows that AI-generated passwords are leaving fingerprints in the wild. In this interview, he explains how he used Markov chains, a century-old statistical model, to detect patterns in passwords generated by modern LLMs, attribute them to model families, and identify 28,000 likely LLM-generated passwords across public GitHub. The findings are a warning for teams adopting AI coding agents.
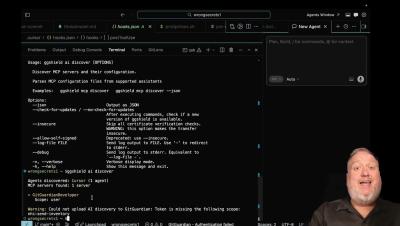
Announcing some major updates in GitGuardian's ggshield version 1.50
This video walks you though some major highlights.
Beyond Detection: What a National Cyber Drill Reveals About True Cyber Resilience
In today’s threat landscape, cybersecurity is no longer defined by the ability to detect and respond to isolated incidents. It is defined by how organizations perform under pressure, when faced with coordinated, AI-enabled, multi-vector attacks that test not only technology, but leadership, governance, and trust. Recently, Obrela had the opportunity to support a national-level cyber security drill in Qatar, working alongside our partner ecosystem.
From pilot to Moderate: Lessons from Vanta's FedRAMP 20x journey
Accelerating security solutions for small businesses Tagore offers strategic services to small businesses. A partnership that can scale Tagore prioritized finding a managed compliance partner with an established product, dedicated support team, and rapid release rate. Standing out from competitors Tagore's partnership with Vanta enhances its strategic focus and deepens client value, creating differentiation in a competitive market. Vanta is now FedRAMP 20x Moderate authorized.
Stay Ahead of Attackers with CrowdStrike Falcon
See how CrowdStrike Falcon helps your team detect, investigate, and stop threats across endpoints, identity, and cloud—faster and with less noise.
Accelerating AI Discovery & Governance with the Falcon Platform
As AI adoption accelerates, so does shadow AI. Without a complete inventory of AI tools, agents, and activity, organizations are exposed to unapproved usage and data risk. In this video, you will see how the Falcon platform helps teams: Discover AI tools, models, and services in seconds Identify unapproved and risky usage See where AI is running and what it can access across endpoints Take action and enforce governance at scale.
Navigating the New VMware Reality: What Broadcom's Changes Mean for Your Business
When Broadcom completed its $69 billion acquisition of VMware in November 2023, most customers assumed the initial disruption would settle. Licensing models would stabilise. Partner programmes would find a new equilibrium. Pricing would normalise. Two years in, it’s clear that didn’t happen.
LevelBlue Recognized at Intelligent Insurer's Cyber Insurance Awards US 2026
LevelBlue is proud to be named at the Intelligent Insurer Cyber Insurance Awards US 2026, earning Cyber Security Consulting Services Provider of the Year and being recognized as Highly Commended for the Cyber Security Solution Provider of the Year. These recognitions reflect the continued evolution of the cybersecurity landscape and the growing importance of strong collaboration between insurers, enterprises, and security providers.
The ABCs of KYT: How this key process combats payment fraud
Banks, payment processors and fintechs have long relied on Know Your Customer (KYC) processes to verify identity and assess the risk of doing business with the customer during onboarding, and on Know Your Business (KYB) processes to validate business legitimacy. But today, that’s no longer enough.