Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Just released! AT&T Cybersecurity Insights Report: 5G and the Journey to the Edge
We are certainly in unique times, with COVID driving digital transformation at an unprecedented pace, remote work appearing to be long term, and the specter of new threats looming over security professionals as they strategized how to protect a rapidly changing business and tech landscape. To use perhaps one too many cliches: it is the best of times, it is the worst of times, the times are a changin’, and a change will do you good. No really, it will.
Top tips for better security awareness on the job from Detectify Security Champions
Security is not compliance. This is something that the security champions at Detectify can agree on and each employee practices security everyday to help keep our customers and business secure. You’ve probably never met a more engaged group about security training than us at Detectify! We are passionate about our industry and maybe even gain a few new security nerds every few months as we go.
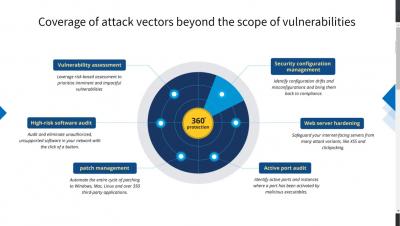
Vulnerability Management with ManageEngine Vulnerability Manager Plus
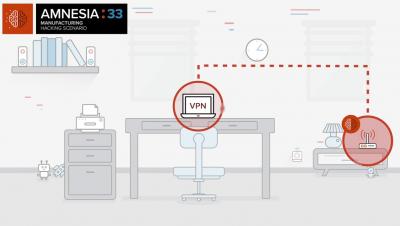
What is AMNESIA:33?
How to identify and mitigate risk from AMNESIA:33 vulnerabilities
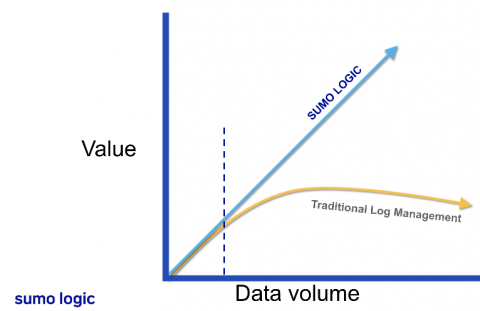
Building your modern cloud SIEM
See Netskope Prove It
Tighten Up Your Strategy: Evaluating the Leakiness of a Cloud App
We at Netskope Threat Labs have published a series of blogs detailing the misconfigurations in cloud apps causing data exposure. Misconfiguration and sensitive data exposure have been listed as predominant top 10 OWASP security risks for years, and are now also the predominant cause of cloud data breaches.
What is Access Control?
Access control is a security technique that regulates who or what can view, use or access a place or other resources. It is a fundamental concept in physical security and information security designed to minimize risk. At a high level, access control is about restricting access to a resource. Any access control system, whether physical or logical, has five main components: Access control can be split into two groups designed to improve physical security or cybersecurity: