Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Demo: WatchGuard AuthPoint and Firebox Integration - VPNs
Lessons From Billions of Breached Records by Troy Hunt of https://haveibeenpwned.com
Innovation lessons we can learn from hackers
5 Vulnerability Assessment Scanning Tools: 5 Solutions Compared
Vulnerability assessments define, identify, classify, and prioritize flaws and vulnerabilities in applications, devices, and networks that can expose organizations, their products, services, code, and applications, to attack. Security vulnerabilities allow malicious actors to exploit an organization’s applications and systems, so it is essential to identify and respond to them before attackers can exploit them.
Cybersecurity Best Practices for the Oil and Gas Industry
What is a watering hole attack?
The advance of the 21st century brought with it a significant shift in the work scene. Every industry and field relies heavily on computers and the digital world to function seamlessly. However, with it came the ever-mounting fear of cyber attack. Among the many forms of cyber attack is a watering hole attack, also known as a supply chain attack. In a watering hole attack, attackers mainly try to compromise a user by infecting the user’s computer and gaining access to the network.
Falcon Fusion Accelerates Orchestrated and Automated Response Time
In the recent MITRE Engenuity ATT&CK Enterprise Evaluation — which emulated today’s two most sophisticated Russian-based adversaries, WIZARD SPIDER and VOODOO BEAR (Sandworm Team) — CrowdStrike Falcon achieved 100% automated prevention across all of the evaluation steps.
#BigPictureCyber Town Hall With Michael McLaughlin, UMD ARLIS | 4/27/22 | NeoSystems
Forward Networks: How to prove network innocence in seconds, even in multi-cloud environments
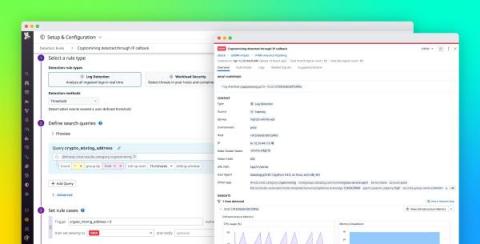
Detect cryptocurrency mining in your environment with Datadog Cloud SIEM
Cryptocurrency mining (or crypto mining) can be a lucrative yet resource-intensive operation, so cyber threat actors are targeting more organizations in order to take advantage of their cloud resources for mining. Datadog Cloud SIEM can now help you monitor your cloud-based systems for unwanted crypto mining via a built-in detection rule. All you need to get started is to configure your resource logs with Datadog’s @network.client.ip standard attribute.