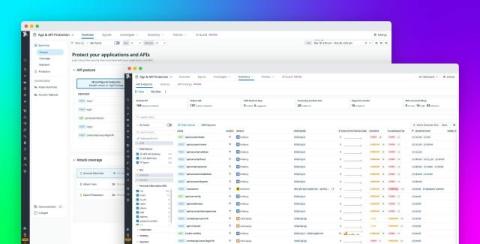
Demo: Access controls for GenAI and agentic AI
See how Cloudflare One simplifies access controls across both generative AI and agentic AI communication — all from one unified secure access service edge (SASE) dashboard. This demo highlights: Securing human-to-AI connections by as blocking or redirecting from unapproved tools and isolating AI apps to protect data (0:09) Streamlining access to MCP servers for AI-to-resource connections via Cloudflare’s MCP server portals (1:10)