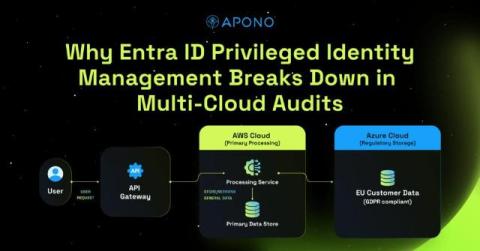
Why Entra ID Privileged Identity Management Breaks Down in Multi-Cloud Audits
For many enterprise security teams, audit season feels less like validation and more like reconstruction. Not because they lack logs, and not because their teams are careless, but because their privilege model was never designed to produce a clean, unified story. In Microsoft Entra ID environments, Privileged Identity Management (PIM), works well as long as your world is entirely Microsoft. But no enterprise operates in a single-vendor bubble.