Smarter Load Balancing for Modern Apps
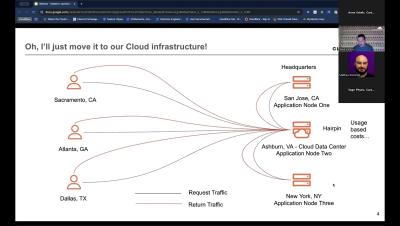
Traditional load balancers weren’t built for today’s distributed applications. As workloads span clouds and regions, you need more flexibility—and fewer bottlenecks. Join us to learn how Cloudflare Load Balancing, powered by our Connectivity Cloud, helps you: Route traffic based on performance, availability, or geography Avoid vendor lock-in and legacy infrastructure limitations Manage all your traffic with a unified set of policies and controls.