Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CrowdStrike Launches Free Targeted Log4j Search Tool
The recently discovered Log4j vulnerability has serious potential to expose organizations across the globe to a new wave of cybersecurity risks as threat actors look to exploit this latest vulnerability to execute their malicious payloads using remote code execution (RCE). An immediate challenge that every organization faces is simply trying to understand exactly where you have applications that are using this very popular Java library — but you are not facing this challenge alone.
Monitoring File Changes with Falcon FileVantage
AWS Live Hack Workshop: Snyk and Atlassian
AWS Live Hack Workshop: Snyk and Terraform
Cloud Security Posture Management
JavaScript type confusion: Bypassed input validation (and how to remediate)
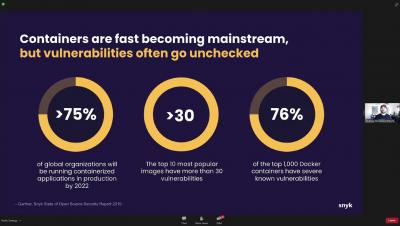
AWS Live Hack Workshop: Snyk and Docker
AWS Live Hack Workshop: Snyk and StackHawk
Third-Party Risk Management Framework: How to Select the Right One
Third-party technology providers can confer huge strategic advantages to a business. It allows each organization to focus on their highest value activities, but there’s a downside; new cyber security risks come with each partnership. Third-party risk is now an integral part of business ecosystems. A solid risk management framework is required to manage risk and keep you and your customers safe.