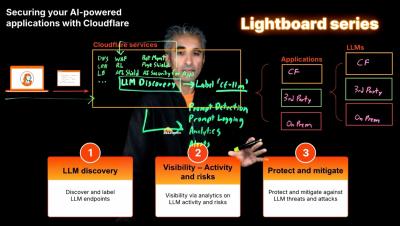
Lightboard series - Secure your AI-powered applications with Cloudflare
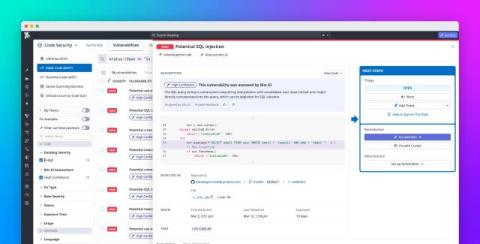
Humair from Cloudflare walks through the details of how Cloudflare's AI Security for Apps secures AI-powered applications. Learn how Cloudflare can discover AI/LLM endpoints and detect and mitigate AI-specific threats like PII exposure, unsafe/toxic content, prompt injection and jailbreak. Learn more.