Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Logsign
Mind the GAAP: A Lens for Understanding the Importance of the CIS Controls
Given that attacks are only increasing and there needs to be greater efficacy in how companies protect themselves, let us reference how the financial industry has created and relies on a body of standards to address issues in financial accounting as a defined comparison for Information Security. To support this argument, there is a defined contrast between information security and Generally Accepted Accounting Principles. We’ll explore this relationship in more detail below.
Appknox
Mend
Defending the client-side attack surface
It is strange to think that not that long ago the Internet was a very different place. A place filled with static text content, marked up in HTML, and served up alongside a few included image files; mostly consumed by a small population of persons with specific interests. Today’s Internet consumer demands a vibrant and responsive user experience customized to their individual interests. A localized cornucopia of options from around the globe, available on demand.
Why SMEs should Care About Cyber Security
It was a turbulent time for business across the globe in 2020 and, whilst the situation is improving in 2021, there are still obstacles to overcome. Not least of all is the ever-present issue of cyber security: an average of 57% of SMEs admit to a breach in 2020, and 86% of organisations expect attacks to increase going forward. As business focus on recovering revenue streams and driving growth, investing in cyber security is often overlooked.
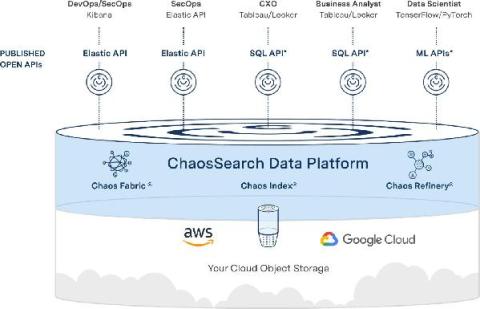
What are the security risks of the cloud computing?
The technological change of the 21st century has seen rapid growth in the innovation and fastest adoption of cloud computing. It is now considered the most ingenious solution that removes the idea of having a data centre by helping businesses meet their needs virtually in the most cost-effective, efficient, and productive way.
What is Threat Modelling? 10 Threat Identity Methods Explained
Threat modelling is a process for identifying potential threats to an organization's network security and all the vulnerabilities that could be exploited by those threats. Most security protocols are reactive - threats are isolated and patched after they've been injected into a system. Threat modelling, on the other hand, is a proactive approach to cybersecurity, whereby potential threats are identified and anticipated.