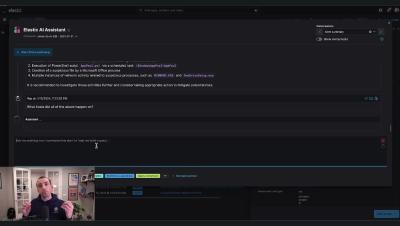
Rolling your own Detections as Code with Elastic Security
From its beginning, the Elastic detection-rules repo not only contained Elastic’s prebuilt detection rules, but also additional tooling for detection rule management — like a suite of tests, CLI commands, and automation scripts used by the Elastic Threat Research and Detection Engineering (TRaDE) team.