Reduce False Positives Automatically with @claude Code and LimaCharlie
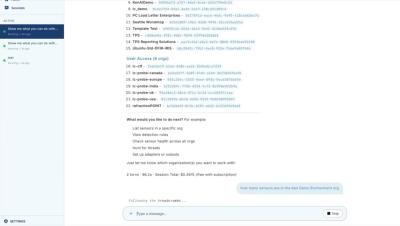
Noisy alerts slow down every SOC. See how Claude Code with LimaCharlie can analyze your existing detection logic and trigger alerts to identify what's generating the noise and what can be done about it. After running the prompt, Claude Code reviews your rules and their trigger frequency, identifies the ones generating false positives, and produces specific recommendations for suppression rules to apply. In this example, it flags three rules and provides the logic to address each one, whether the issue stems from a syntax problem or detection logic that needs tightening.