Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Sysdig Secure and Google Security Command center Integration - Why, What, How
Sysdig is a premier Google Cloud Platform (GCP) partner and has been working with Google towards the common goal of supporting our customers and securing their cloud journey for the last seven years. Sysdig is focused on securing and monitoring workloads running on Google Cloud – including Google Kubernetes Engine (GKE), Autopilot, Anthos, and more. All these various elements of GCP can be protected using Google Security Command Center. Learn more about how to enhance your GCP security.
Sysdig Secure-Google Chronicle Integration - Why, What and How
Cloud adoption and digital transformation have enlarged attack surfaces that can be exploited by malicious actors to harm your organization. Traditional SIEMs and EDRs fall short as they are not cloud-native and also difficult to scale. Further, there are inherent fixed costs that need to be considered when adopting any modern threat detection apparatus.
Comparing GuardDuty & Falco on EKS
Security in cloud providers like AWS is usually the highest priority. With EKS, unlike bring-your-own vanilla Kubernetes instances, you benefit from a data center and network architecture that is built to meet the requirements of the most security-sensitive organizations. To achieve this, one of the best ways is to use all the security layers we are capable of having. In this case, we will explain how to use GuardDuty and Falco to speed up threat detection.
Discovered new BYOF technique to cryptomining with PRoot
The Sysdig Threat Research Team (TRT) recently discovered threat actors leveraging an open source tool called PRoot to expand the scope of their operations to multiple Linux distributions and simplify their necessary efforts. Typically, the scope of an attack is limited by the varying configurations of each Linux distribution. Enter PRoot, an open source tool that provides an attacker with a consistent operational environment across different Linux distributions, such as Ubuntu, Fedora, and Alpine.
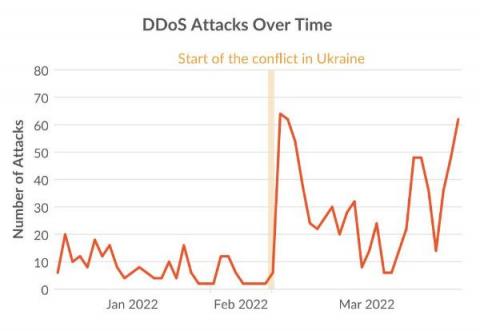
How the Russia-Ukraine conflict changed cyber attacks: More attacks, More DDoS
The conflict between Russia and Ukraine includes a cyberwarfare component with government-supported threat actors and civilian hacktivists taking sides. The goals of disrupting IT infrastructure and utilities have led to a 4-fold increase in DDoS attacks between 4Q21 and 1Q22. Over 150,000 volunteers have joined anti-Russian DDoS campaigns using container images from Docker Hub.
Extortion in Cloud Storage
Extortion can simply be defined as “the practice of obtaining benefit through coercion.“ Data and cloud extortion schemes occur when precious data and/or access is stolen by an attacker that promises to restore it through payment or other demands. In this article, we’ll cover some common or uncommon extortion schemes, and highlight ways to detect and avoid falling prey to demands.
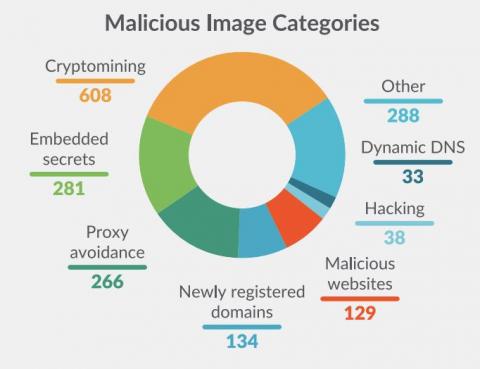
Analysis on Docker Hub malicious images: Attacks through public container images
Supply Chain attacks are not new, but this past year they received much more attention due to high profile vulnerabilities in popular dependencies. Generally, the focus has been on the dependency attack vector. This is when source code of a dependency or product is modified by a malicious actor in order to compromise anyone who uses it in their own software.
How to secure Docker Containers - Container Security Best Practices
CSPM - Least privilege principle in practice
Cloud Security Posture Management (CSPM) aims to automate the identification and remediation of risks across your entire cloud infrastructure. A core requirement of the CSPM framework is the need to enforce a principle of least privilege. There are certain overlaps with Cloud Infrastructure Entitlement Management (CIEM) solutions. CIEM is a newer categorization that came after CSPM.