How to set up SAML Authentication for IDP?
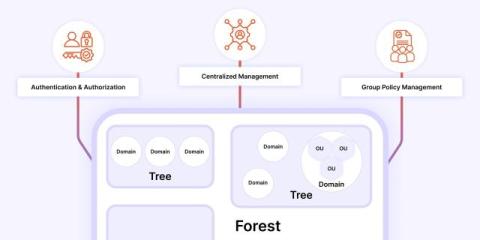
Learn How to Set Up SAML Authentication for Your Identity Provider Using CASB In this step-by-step tutorial, we’ll walk you through setting up SAML authentication with your Identity Provider (IdP) using a Cloud Access Security Broker (CASB) via the miniOrange dashboard. What You’ll Learn: Why Use CASB with SAML? CASB adds a layer of visibility and control for your cloud services. Combined with SAML authentication, you get centralized, secure, and compliant user access management across your cloud apps.