Coffee Talk with SURGe!
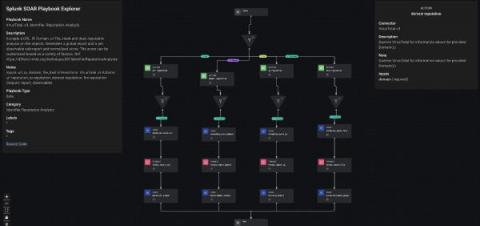
Grab a cup of coffee and join Mick Baccio and Audra Streetman for another episode of Coffee Talk with SURGe. The team from Splunk will discuss the latest security news, including: Mick and Audra also shared their stance on AI regulation as part of this week's 60 second charity challenge, with proceeds benefitting the Save Elephant Foundation.