Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The latest News and Information on Security Incident and Event Management.
Are disconnected RDP sessions ticking time bombs in your network?
I think we’ve all been there before – you log on to a server remotely via RDP, and do the needful – but don’t immediately log off. But then you get distracted by a phone call, an email, a chat, or a good old-fashioned physical interaction with another human being. So when it comes time clock out for the night, you shut down your computer or log off. Or maybe you’ve been working on a laptop and your VPN got interrupted.
Why you need both SIEM and SOAR to improve SOC efficiencies and increase effectiveness
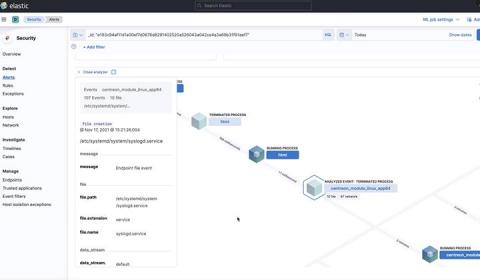
Protect your AWS workloads using Elastic Security
It’s no secret that cloud service providers like AWS, Google Cloud, and Azure give teams incredible power and flexibility when it comes to delivering great solutions and user experiences to a global customer base. Leveraging the power of one or more clouds is often seen as a critical competency for an organization to succeed.
Automated Vulnerability Scan To Protect Your Business
A vulnerability scan is an automated process that identifies vulnerabilities (security holes) in any software, operating system, or network that bad actors can exploit. In essence, it’s an integral component of vulnerability management focused on protecting businesses from breaches and the exposure of sensitive data.
Multi-tenant Cloud Architecture
Today organizations have been able to recognize over the years the benefits of implementing a Cloud-based SIEM Service in terms of scalability, cost, and security. However, before operating in the cloud, you should know what architecture you need to adopt to protect your business and your customers’ data. Intending to help you implement a cost-effective SaaS SIEM Service, we share the advantages of multi-tenant over a single-tenant cloud architecture.
An Overview of UTMStack Features.
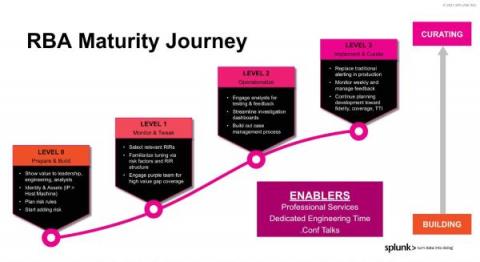
Risk-Based Alerting: The New Frontier for SIEM
If you haven't heard the gospel of risk-based alerting (RBA) in a SIEM context, by the end of this sermon you'll see why you’ll want it running in your environment yesterday, whether you're an analyst, an engineer, or in leadership.
Elastic Protects Against Ransomware and Linux Threats in MITRE Engenuity Round 4 Eval
That’s right all, it’s time for the latest MITRE Engenuity ATT&CK® evaluation. As we have come to expect each year, Elastic — along with other security vendors — are evaluated by MITRE Engenuity, a tech foundation that brings MITRE research to the public. The evaluation focuses on emulating techniques from the MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) framework to assess vendor protection capabilities.
4 golden reasons for equipping your SOC with ManageEngine Log360
Cyberattacks are fast becoming a part of our daily lives. Multiple sources such as Norton Security and Forbes suggest that since the pandemic, attacks are not only increasing in number, but they are becoming more targeted and sophisticated. The attackers using Ransomware as a Service and double extortion techniques are prime examples of how sophisticated attacks are becoming these days. Norton Security states that there are more than 2,200 cyberattacks on a daily basis.