Exploits, vulnerabilities and threat adaptation
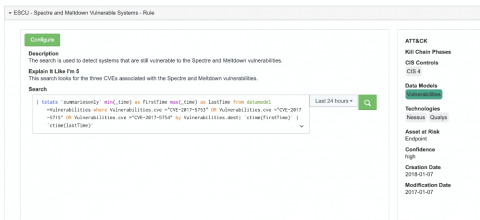
Security, whether focused on physical, cyber, operational, or other domains, is an interesting topic that lends itself to considerable debate among practitioners. There are, however, basic concepts and underpinnings that pervade general security theory. One of the most important, yet often misunderstood concepts are those inextricably entwined concepts of vulnerabilities and exploits. These basic underpinnings are critical in all security domains.