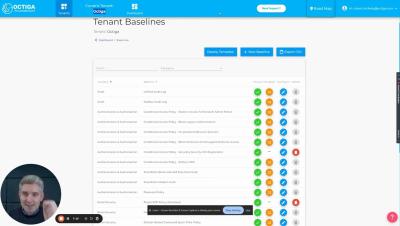
Introducing security controls into cloud deployment
We’re excited to share an insightful video where our Co-Founder and CTO Avishai Wool delves into the critical topic of "Introducing Security Controls into Cloud Deployment." Avishai shares proven strategies to integrate robust security controls into your cloud deployment strategy. Gain exclusive insights and discover how cutting-edge technologies are shaping the future of cloud security.