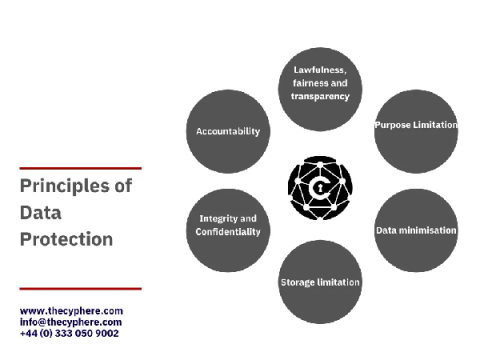
The 8 principles of The Data Protection Act & GDPR
The Data Protection Act 2018 is the legislation enforced by the Information Commissioner’s Office (ICO), UK, to protect personal data processing and data stored on the computer, digital media, or paper filing systems.