Predicting which hackers will become persistent threats
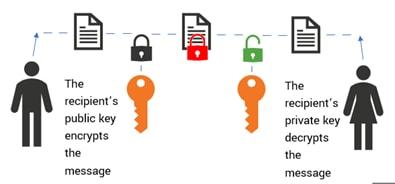
Websites are central to business operations but are also the target of various cyber-attacks. Malicious hackers have found several ways to compromise websites, with the most common attack vector being SQL injection: the act of injecting malicious SQL code to gain unauthorized access to the server hosting the website. Once on the server, the hacker can compromise the target organization's website, and vandalize it by replacing the original content with content of their own choosing.