A Beginner's Guide to Service Accounts: What They Are and How To Secure Them
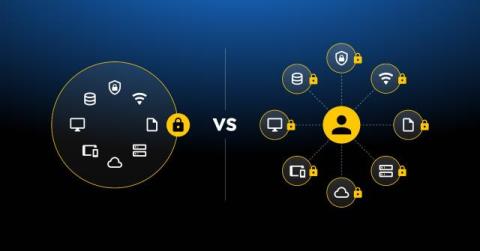
Service accounts are nonhuman privileged accounts used by systems or applications to perform certain tasks, access resources or run processes. These accounts are typically given only the permissions they need for a specific job. According to ReliaQuest, 85% of data breaches between January 2024 and July 2024 that organizations responded to involved compromised service accounts. To prevent the misuse of credentials, organizations should secure their service accounts.