Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
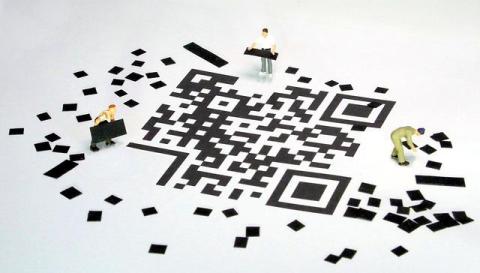
Securing QR Codes: Protect Against Cyber Threats
QR codes have become part of daily life, enabling quick access to websites and services with a single scan. However, this convenience also makes them a major target for cybercriminals who exploit their popularity. The hidden nature of QR data can easily redirect users to malicious content or phishing sites without their knowledge. With the growing risks tied to this technology, businesses need to implement more advanced security measures. Simple practices like regularly checking code destinations and verifying source authenticity can help reduce vulnerabilities.
Kubernetes Namespace Restriction and Separation
Teleport provides a secure and scalable solution for managing namespace separation in Kubernetes clusters, streamlining compliance, and enabling financial institutions to maintain both resiliency and agility. Kubernetes has rapidly evolved from a tech buzzword to an indispensable backbone of modern infrastructure in the financial services industry — redefining how institutions scale, secure, and deliver their most critical applications.
Web Application Security for DevOps: The Fundamentals
Writing reliable and user-friendly web applications takes significant knowledge, skill, and experience; writing secure web applications introduces a whole new level of complexity.
Responsible AI: Policy Solutions for DevSecOps
Artificial intelligence (AI) is revolutionizing problem-solving and innovation in DevSecOps. Leveraging AI responsibly is essential for building secure, trustworthy systems. Governments are crafting policies to ensure AI's benefits while mitigating risks. Join JFrog's VP of Product Marketing, Jens Eckels, and BSA CEO, Victoria A. Espinel, as they explore how BSA’s Policy Solutions for Building Responsible AI provides a framework to achieve these goals, focusing on governance, innovation, and transparency.
The importance of CSPM inventory
Almost all organizations either rely on cloud computing or are planning to adopt cloud computing technologies soon to ensure their businesses remain competitive and gain an edge over the competition. As businesses increasingly rely on cloud services to manage their operations, the complexity of these environments continues to grow, introducing new challenges in maintaining security and compliance. This is where Cloud Security Posture Management (CSPM) comes into the picture.
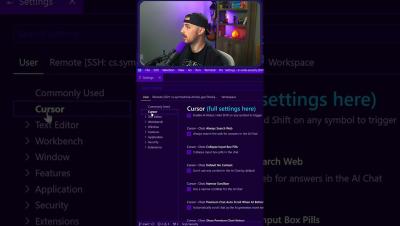
Cursor AI: The VS Code Competitor
Cursor AI is a new AI-powered code editor that some say could be the VS Code KILLER... In this video, we will be putting that to the test by exploring the AI tool's features as well as using it to help with our code in building a notes API and UI.