Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Preventing Recent Microsoft Exchange Vulnerabilities and Similar Attacks Using Netskope Private Access
On March 2, Microsoft released patches to address four zero-day vulnerabilities in Microsoft Exchange Server software. Those vulnerabilities, known collectively as ProxyLogon, affect on-premises Exchange Server 2013, Exchange Server 2016, and Exchange Server 2019. (Exchange Online, which is part of Microsoft 365, has not been affected.)
Detect suspicious activity in GCP using audit logs
GCP audit logs are a powerful tool that track everything happening in your cloud infrastructure. By analyzing them, you can detect and react to threats. Modern cloud applications are not just virtual machines, containers, binaries, and data. When you migrated to the cloud, you accelerated the development of your apps and increased operational efficiency. But you also started using new assets in the cloud that need securing.
Cloud lateral movement: Breaking in through a vulnerable container
Lateral movement is a growing concern with cloud security. That is, once a piece of your cloud infrastructure is compromised, how far can an attacker reach? What often happens in famous attacks to Cloud environments is a vulnerable application that is publicly available can serve as an entry point. From there, attackers can try to move inside the cloud environment, trying to exfiltrate sensitive data or use the account for their own purpose, like crypto mining.
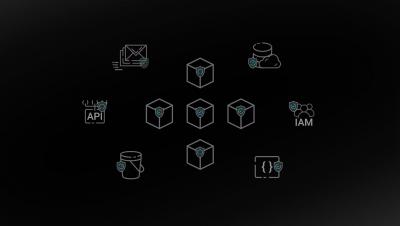
Unified threat detection for AWS cloud and containers
Implementing effective threat detection for AWS requires visibility into all of your cloud services and containers. An application is composed of a number of elements: hosts, virtual machines, containers, clusters, stored information, and input/output data streams. When you add configuration and user management to the mix, it’s clear that there is a lot to secure!
Getting started with cloud security
Getting started with Teleport Application Access
0:00 Intro
1:09 Docker Setup & Grafana setup
2:27 Setup and Install Teleport
4:33 teleport configure
5:30 teleport start
6:12 tctl users add & Local user setup
7:00 Accessing Grafana via Teleport
7:58 Conclusion
RFD 14 Demo - Per-session MFA
This video is a demo of our per-session MFA coming in Teleport 6.1 https://github.com/gravitational/teleport/blob/master/rfd/0014-session-2FA.md#rfd-14---per-session-mfa