Eliminating Privileged Access Toil with Infrastructure Identity
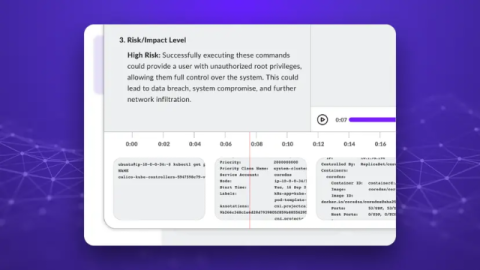
Modern infrastructure is dynamic, ephemeral, and complex, with new technology (such as agentic AI) constantly being added. However, disjointed and unsecured AI and human identities introduce risk through social engineering, credential theft, and prompt hacking, as well as complexity and toil for engineering teams.