Can You Kill an API Token in Real Time? Here's Why It Matters #apikeys #api #incidentresponse
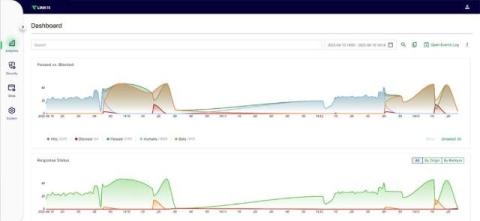
What happens if an API token or key is compromised? The ability to instantly revoke or block tokens during an incident is critical to stopping attackers. In this clip, Wallarm and Oracle experts discuss real-world challenges in detecting and disabling malicious tokens—and why mature incident response and tooling are essential for API security.