Support Universal ZTNA with Netskope One Private Access
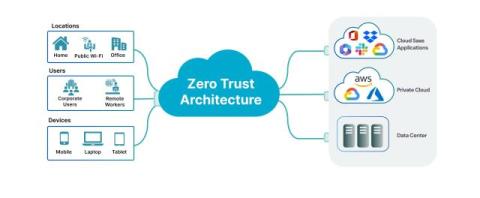
As hybrid work becomes the norm, it’s clear that traditional virtual private networks (VPNs) and network access control (NAC) solutions are falling short. Once the gold standard for secure remote access, VPNs now pose more problems than solutions—think slow performance, security risks, and complex operations.