The dark web : what threat does this pose to your company?
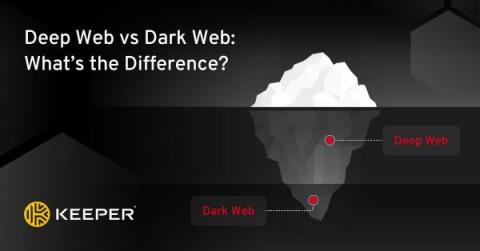
There is a welter of websites that are not indexed by search engines on the dark web, making it an ideal space to exchange all kinds of illegal content or products. This dark part of the web actually represents just 0.1% of the deep web. So how come something so small can be so dangerous for organizations and users?