Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to detect security threats in your systems' Linux processes
Almost all tasks within a Linux system, whether it’s an application, system daemon, or certain types of user activity, are executed by one or more processes . This means that monitoring processes is key to detecting potentially malicious activity in your systems, such as the creation of unexpected web shells or other utilities.
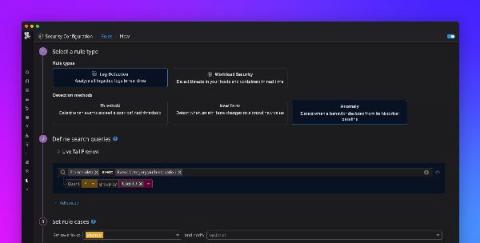
Detect security threats with anomaly detection rules
Securing your environment requires being able to quickly detect abnormal activity that could represent a threat. But today’s modern cloud infrastructure is large, complex, and can generate vast volumes of logs. This makes it difficult to determine what activity is normal and harder to identify anomalous behavior. Now, in addition to threshold and new term –based Threat Detection Rules , Datadog Security Monitoring provides the ability to create anomaly
Highlights from Black Hat USA 2021
Black Hat USA is one of the industry’s oldest and most well-established security events. Last year, the conference was held virtually for the first time in its history. This year’s conference brought together the best of both worlds, with a hybrid event that was held virtually and in person in Las Vegas. Historically, Black Hat has seen about 20,000 attendees at its in-person conference.
Monitor AWS FSx audit logs with Datadog
Amazon FSx for Windows File Server is a fully managed file storage service built on Windows Server. Migrating on-premise Windows file systems to a managed service like FSx enables organizations to reduce operational overhead and take advantage of the flexibility and scalability of the cloud. But having visibility into file access activity across their environment is key for security and compliance requirements, particularly in sectors such as financial services and healthcare.
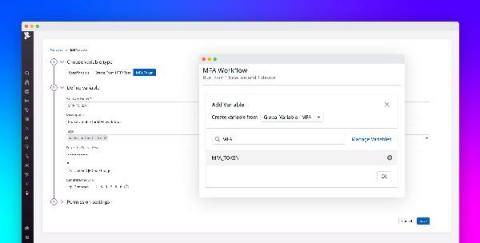
Introducing multi-factor authentication in Datadog Synthetic tests
Multi-factor authentication (MFA) is an increasingly popular method for securing user accounts that requires users to provide two or more pieces of identifying information when logging into an application. This information can consist of unique verification links or codes sent to the user’s phone or email address, as well as time-based one-time passwords (TOTPs) generated by authenticator applications or hardware.
Key takeaways from the U.S. executive order on cybersecurity
On May 12, 2021, President Biden signed an executive order calling on federal agencies to improve their cybersecurity practices. Following the recent SolarWinds and Colonial Pipeline attacks, it is clear that security incidents can severely impact the economy and civilians' day-to-day lives and that cybersecurity needs to be a high-priority issue. We encourage you to read the full executive order.
Resilience, DevSecOps, and other key takeaways from RSAC 2021
For the first time in its 30-year history, the 2021 RSA Conference was a virtual-only event, and not in its usual time during the spring. But, with 20,000 registrants joining for the various sessions, it was a testament to this year’s conference theme of resilience.
Measure your DevSecOps maturity with Datadog's self-assessment
With DevOps teams moving at ever greater speed, it’s vital for security teams to be deeply involved at all stages of the software development and delivery lifecycle. Breaking down silos between development, operations, and security teams ensures that security considerations are not overlooked, that vulnerabilities are caught early, and that security checkpoints do not slow down the delivery process.
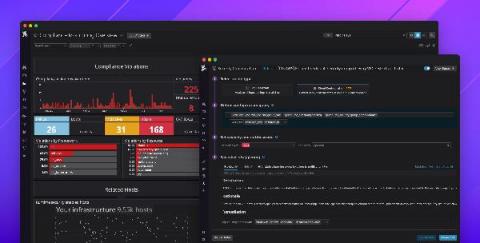
Introducing Datadog Cloud Security Posture Management
Governance, risk, and compliance (GRC) are major inhibitors for organizations moving to the cloud—and for good reason. Cloud environments are complex, and even a single misconfigured security group can result in a serious data breach. In fact, misconfigurations were the leading cause of cloud security breaches in 2020. This puts a lot of pressure on developer and operations teams to properly secure their services and maintain regulatory compliance.