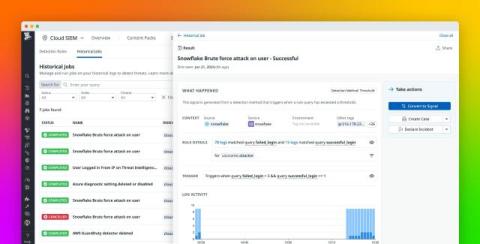
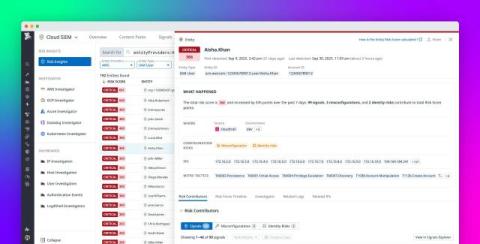
Monitor the security of your Snowflake instance with Datadog Cloud SIEM
Snowflake is a fully managed data platform that enables users to store, process, and analyze large volumes of data across their cloud environments. Recently, Datadog’s Security Research Team posted a threat hunting guide to help defenders ensure the security of their Snowflake instances.