Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
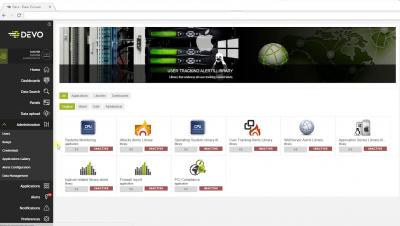
Monitoring Unix Machines with Devo
Tripwire Products: Quick Reference Guide
Here at The State of Security, we cover everything from breaking stories about new cyberthreats to step-by-step guides on passing your next compliance audit. But today, we’d like to offer a straight-forward roundup of the Tripwire product suite. Get to know the basics of Tripwire’s core solutions for FIM, SCM, VM and more. Without further ado…
Catching Configuration Changes that Can Lead to Data Exposure
Amazon’s new security issue, which came to light just days before one of its biggest sale events of the year, is making recent headlines. And whilst it probably won’t stop the online retail giant from achieving a profitable Black Friday and Cyber Monday this year, it certainly will make many users stop and think.
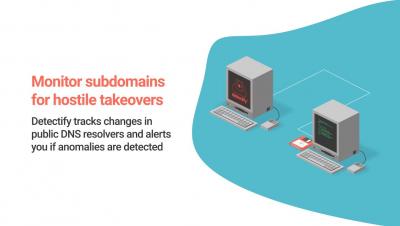
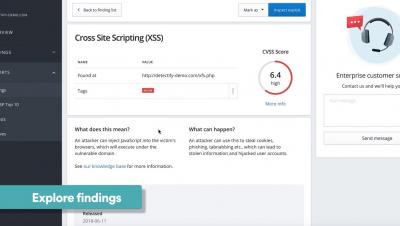
Detectify for security teams
Getting started with Detectify
Choosing an Industrial Cybersecurity Framework
Tripwire Data Collector Increases Operational Technology Visibility With Enhanced Web Scripting Capability
Tripwire Data Collector has been providing industrial organizations with visibility into their operational technology (OT) environments since its release in mid-2018.