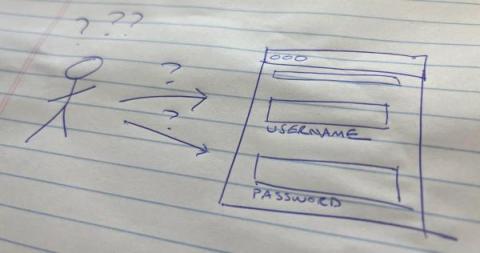
My Username Fields Have Passwords in Them! What Do I Do?
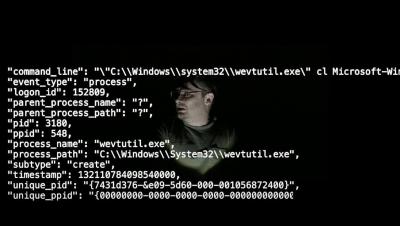
As security practitioners, we like to read blogs, whitepapers, and even Mastodon “toots” that talk about new or novel threats and vulnerabilities. Recently, our fearless and never sleeping Security Strategist Leader James Brodsky called attention to a blog post from a researcher that highlighted the risks of password disclosure in authentication logs.