Implementing AI within your security strategy: 7 best practices
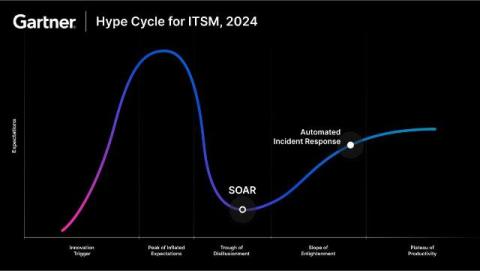
There’s a ton of media hype about the swift integration of AI across different business functions. It has also been reported that 98% of technology executives have paused their AI programs to establish guidelines and policies around its implementation. Depending on when and where you read about it, opinions on the speed of AI adoption vary. Nevertheless, AI is more than just hype.