Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Role of Managed Detection and Response - State of Incident Response 2021
Kroll's 2-Minute Snapshot: The Role of Regulation in Life Sciences
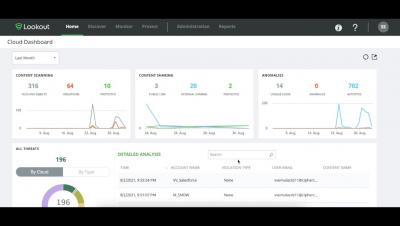
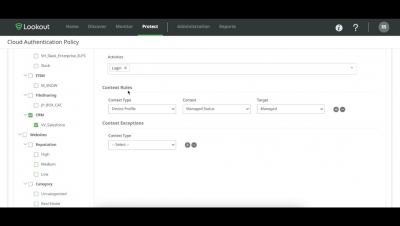
PM Walkthrough: Lookout Continuous Conditional Access integration with CASB & ZTNA
Demo: Lookout Continuous Conditional Access integrates with CASB and ZTNA
Microsoft Power Apps Data Leak // Webinar
How to increase & justify your cybersecurity budget
Microsoft Office Document Triggering New Zero-Day
Most ransomware groups operating in the RaaS (Ransomware-as-a-Service) model have an internal code of A new zero-day vulnerability (CVE-2021-40444) affecting multiple versions of Windows has recently been discovered and disclosed by Microsoft. According to Microsoft’s Security Update Guide, the MSHTML component can be exploited by an attacker through a custom ActiveX control, allowing remote code execution.
Where Should We Draw the Cyber Blue Line?
What are the limits of online privacy and law enforcement? Can we clearly define them, or is this a vague and blurred area of debate? The fact is that as technology advances, the real and the virtual worlds are increasingly converging. Actions (or inactions) in the cyberspace introduce risks and threats for people, especially the most vulnerable ones, i.e. children and elders.
Collaborate Seamlessly with Egnyte and Google Workspace
Today’s organizations utilize a multitude of solutions to create, share and manage their sensitive content. That business reality is exacerbated by additional cloud file storage solutions that result from acquisitions, competing employee preferences, or shadow IT initiatives. So, it’s no surprise IT teams struggle to manage and control document and file system sprawl.