Why the World's Top MSSPs are Ditching Legacy SOAR for Hyperautomation
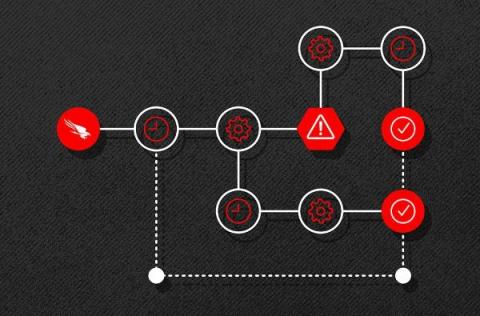
Managed Security Service Providers (MSSPs), desperate to automate repetitive tasks, initially turned to SOAR to reduce their workload and improve threat response times. Unfortunately, legacy SOAR tools still face scalability, flexibility, and integration challenges. As the complexity and volume of cyber threats continue to grow, the limitations of legacy SOAR have become more apparent, necessitating the move towards more advanced automation technologies like Torq Hyperautomation.