Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
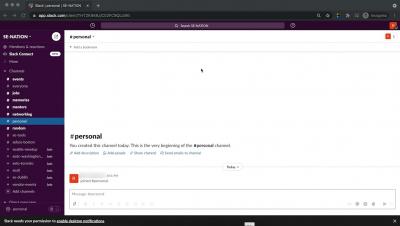
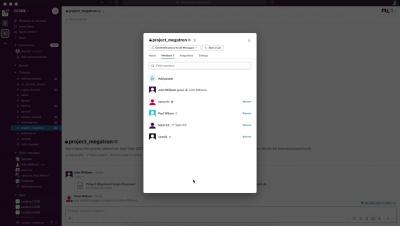
Lookout CASB - Preventing Sensitive Data Leakage to Personal Channels in Slack
Lookout CASB - Secure Collaboration and Compliant Sharing of Content in Slack
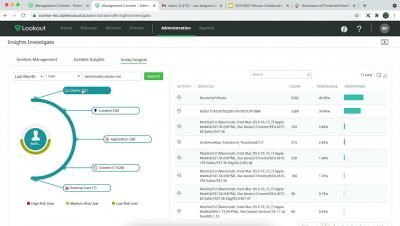
Lookout CASB provides enhanced visibility into activities in Slack
Protecting Users from Malicious Sites with Falcon for Mobile
Lookout Data Shows Already Strained Energy Industry Faced With 161% Surge in Mobile Phishing
A few months ago, the largest U.S. pipeline operator, Colonial Pipeline, was forced to halt operations for nearly a week due to a ransomware attack. While it ultimately didn’t stop consumers from buying gasoline, the incident forced the company to pay $4.4 million in ransom payment and illustrated just how vulnerable energy organizations are to cyberattacks.
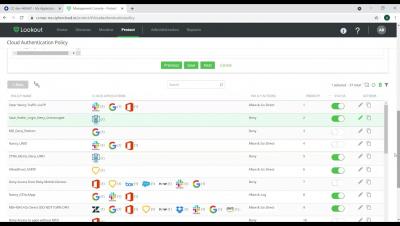
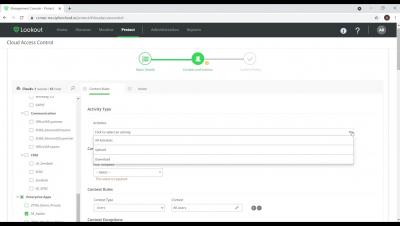
Lookout ZTNA - Creating Policies for data protection and application security
Lookout CASB Protects your Business
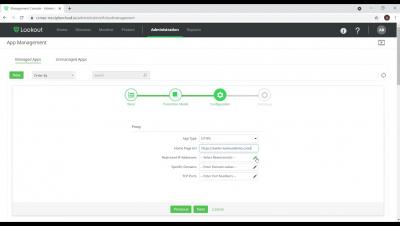
Lookout ZTNA - Intro to onboarding an application, securing access and protecting sensitive data.
Rooting Malware Makes a Comeback: Lookout Discovers Global Campaign
Security researchers at the Lookout Threat Lab have identified a new rooting malware distributed on Google Play and prominent third-party stores such as the Amazon Appstore and the Samsung Galaxy Store. We named the malware “AbstractEmu” after its use of code abstraction and anti-emulation checks to avoid running while under analysis. A total of 19 related applications were uncovered, seven of which contain rooting functionality, including one on Play that had more than 10,000 downloads.