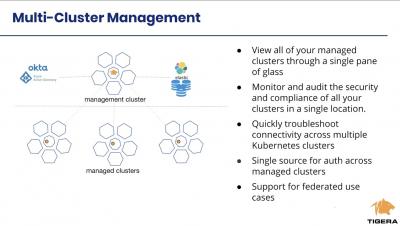
Calico Enterprise Multi Cluster Management - Federated Identity and Services
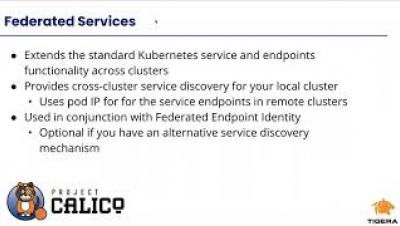
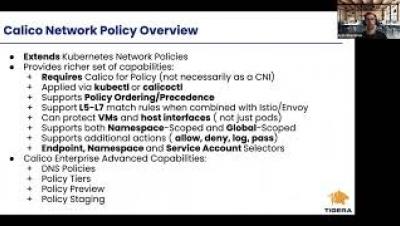
Learn how to simplify deployment and ongoing operations for more than one cluster running Calico Enterprise. What is Calico Enterprise Multi-Cluster Management How is Calico Enterprise Multi-Cluster architected How to set up Calico Enterprise Multi-Cluster Management How to enable Federated Endpoint Identity and Services for Multi-Cluster use cases A Calico Enterprise trial is available after this session and you will be able to practice these use cases on your own within a hosted lab.